Evolving Threats in Crypto: The Rise of Supply Chain Attacks
The decline in crypto hacks signals improved security, yet supply chain attacks are emerging as a new challenge. As the industry matures, understanding these evolving threats is essential for comprehensive risk management.
Key Takeaways
- 1## Declining Hack Frequency Masks Evolving Security Challenges The cryptocurrency industry is experiencing a significant drop in successful hacks, indicating progress in foundational security measures.
- 2However, security experts caution that the threat landscape is fundamentally changing, with supply chain attacks emerging as a new frontier of vulnerability.
- 3## Traditional Vulnerabilities Give Way to New Threats Recent data reveals a decline in conventional code-level vulnerabilities that have historically plagued blockchain protocols and decentralized applications.
- 4This trend reflects the industry's maturation in security practices, driven by the increasing adoption of rigorous audit protocols across major platforms.
- 5Despite these advancements, the crypto ecosystem is now contending with a new class of threats.
Declining Hack Frequency Masks Evolving Security Challenges
The cryptocurrency industry is experiencing a significant drop in successful hacks, indicating progress in foundational security measures. However, security experts caution that the threat landscape is fundamentally changing, with supply chain attacks emerging as a new frontier of vulnerability.
Traditional Vulnerabilities Give Way to New Threats
Recent data reveals a decline in conventional code-level vulnerabilities that have historically plagued blockchain protocols and decentralized applications. This trend reflects the industry's maturation in security practices, driven by the increasing adoption of rigorous audit protocols across major platforms.
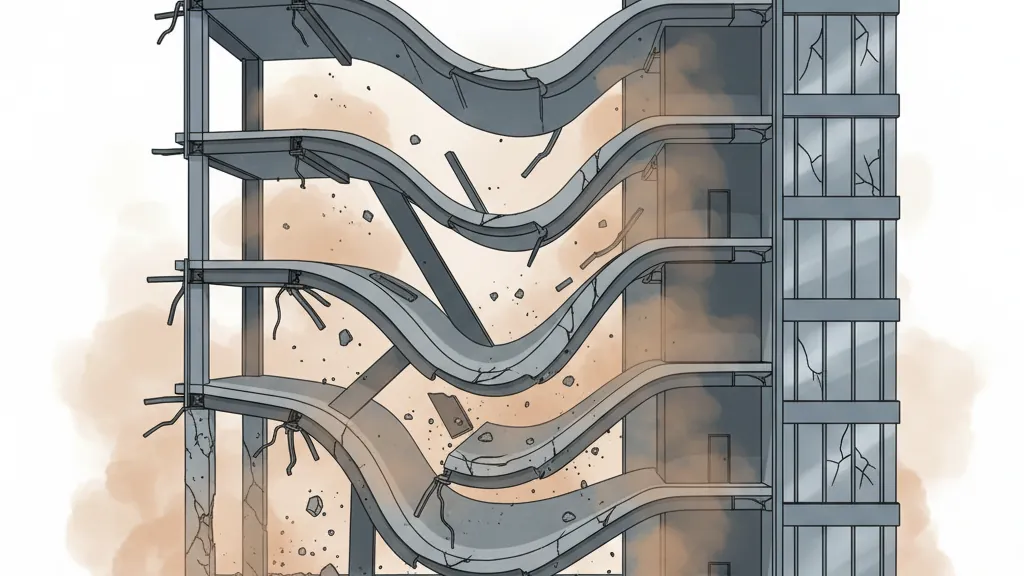
Despite these advancements, the crypto ecosystem is now contending with a new class of threats. Supply chain attacks—targeting the dependencies, libraries, and third-party services that protocols rely on—are reshaping how security professionals approach risk management. Unlike traditional attacks, these exploit trust relationships within the development ecosystem rather than direct code weaknesses.
Sophistication of Scam Tactics Increases
In tandem with the evolution of attack vectors, malicious actors are employing more sophisticated scam tactics. No longer relying solely on technical exploits, bad actors are leveraging social engineering, advanced phishing techniques, and complex schemes that blur the lines between legitimate and fraudulent activities. This trend highlights that while protocols themselves are becoming more secure, the human elements and interconnected nature of the crypto ecosystem continue to present vulnerable points of attack.
Improving Protocol Security
On a positive note, overall protocol security continues to strengthen across the cryptocurrency landscape. Development teams are now implementing more comprehensive security frameworks, conducting regular audits, and adopting best practices, which have significantly reduced exploitable weaknesses at the core protocol level. This enhancement of fundamental security infrastructure has directly contributed to the declining number of hacks, demonstrating that sustained investment in security measures yields tangible results.
Implications for the Industry
The shifting threat landscape necessitates a strategic recalibration of security priorities. While the decrease in successful hacks is promising, the industry must now address supply chain integrity and user-facing attack vectors with the same rigor that was previously applied to smart contract security. Organizations will need to broaden their security frameworks beyond code audits, including comprehensive vetting of dependencies, enhanced monitoring of third-party integrations, and improved user education to combat increasingly sophisticated scams.
Conclusion
The cryptocurrency industry is exhibiting clear signs of maturation, with falling hack numbers reflecting genuine progress in protocol-level protections. However, the emergence of supply chain attacks and advanced scams indicates that the battle for security is not over; rather, it is being fought on new fronts.
Why It Matters
For Traders
Understanding the shift in security threats can help traders make informed decisions about asset risk and security measures involved in trading platforms.
For Investors
Investors should recognize that while security improvements are evident, the industry’s evolving vulnerabilities, particularly supply chain risks, may impact long-term investment stability.
For Builders
Developers must adapt to new threat vectors by prioritizing supply chain security and user education to protect their projects and maintain user trust.